Gain Runtime App Security in the AI Era
Miggo’s Application Detection & Response: The AI runtime defense platform for your applications

Tool Tip
Tools should work where you do. Connect the tools you already use.

Tool Tip
Full visibility is critical. Quickly understand how every 1st and 3rd party application is connected and where sensitive data flows.

Tool Tip
Prioritize threats with runtime context like internet exposure, and exploitability to reduce time spent chasing false positives.

Tool Tip
Security should go beyond alerts. Miggo maintains the cohesive evidence required to triage quickly and respond fast.

Tool Tip
Stay protected with continuous application behaviors monitoring and automated alerts of anomalous activity.
Trusted by Industry Leaders
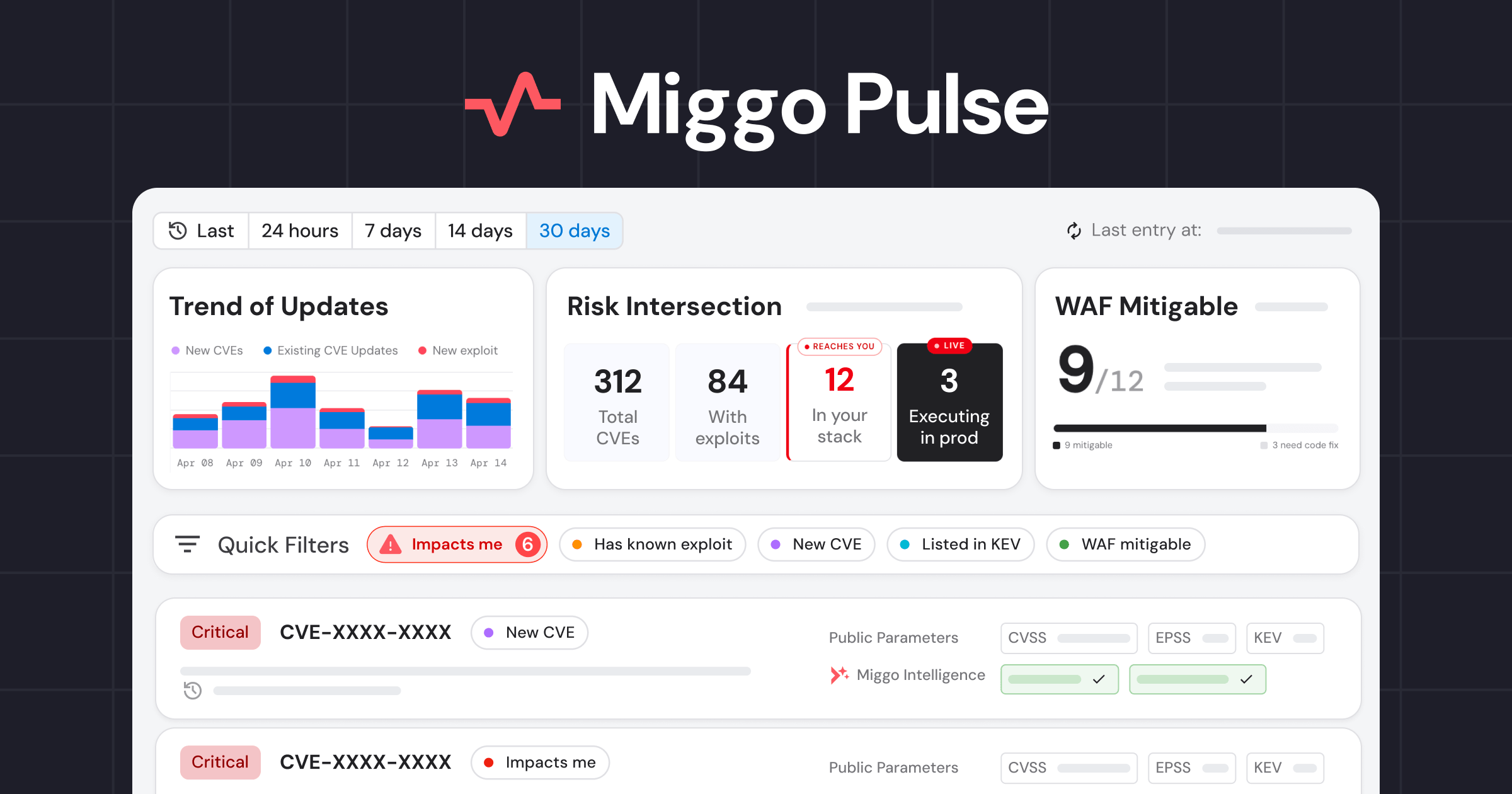
Know what’s live. Prove what matters. Shield in minutes.
Miggo Know
Maintain Full Runtime Application Visibility
Instantly understand how every 1st and 3rd party application is connected within your environment. Gain comprehensive runtime insights with rich context around applications, including internet reachability, drift detection, and sensitive data flows.
Miggo Prove
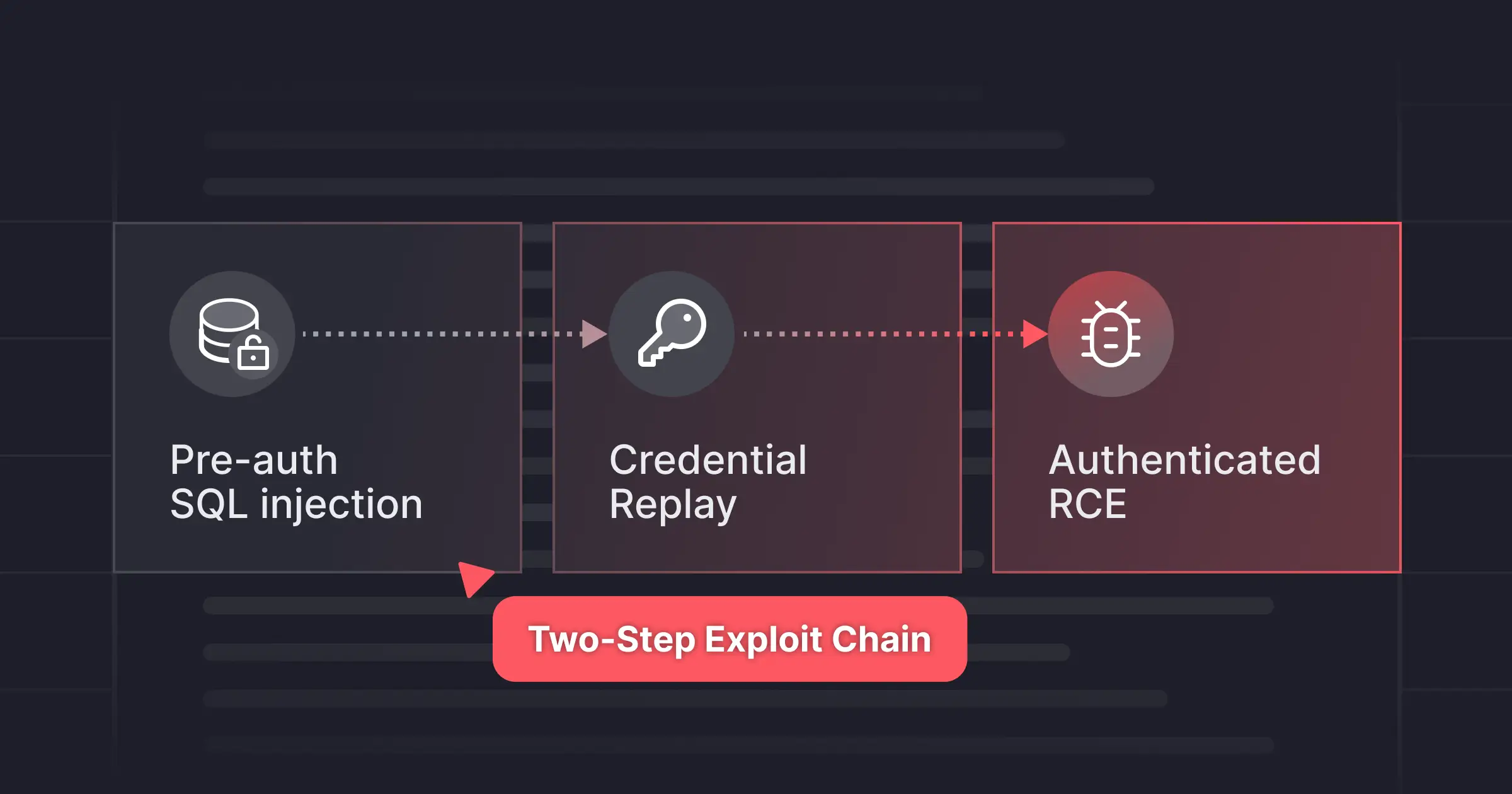
Evidence-Based Runtime Vulnerability Prioritization
Powered by runtime validation and attack-path exploitability, Miggo proves which services and dependencies are truly at risk from AI attackers — surfacing only the vulnerabilities that matter, with clear evidence for both security and development teams.
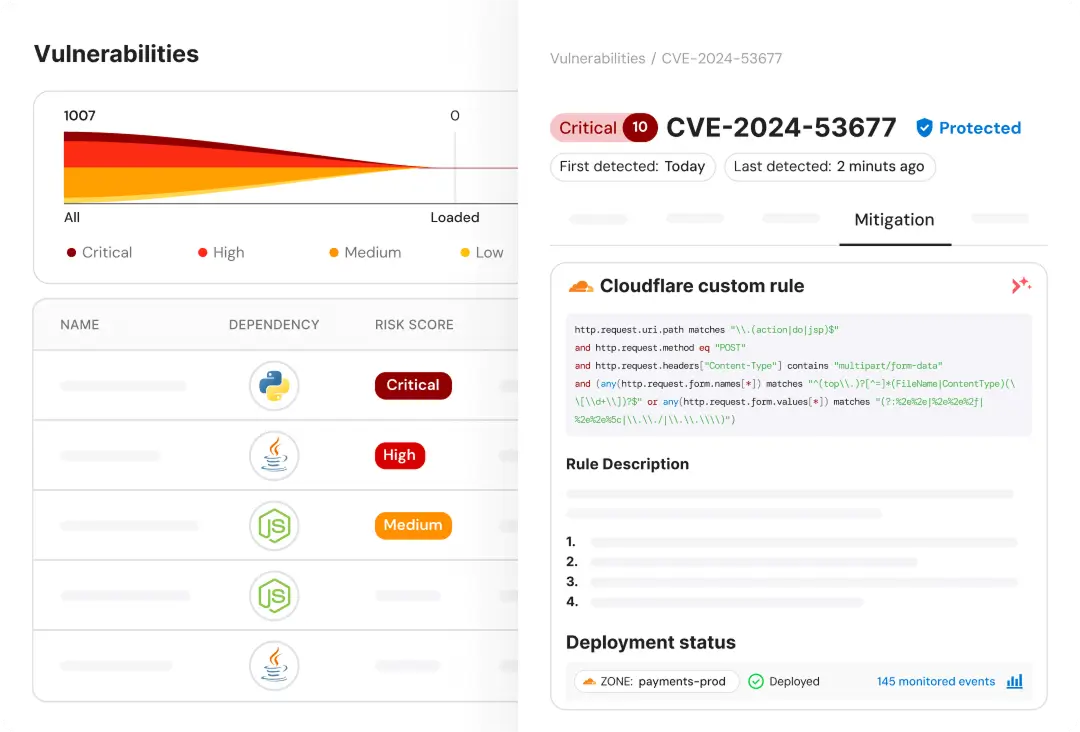
Miggo Shield
1-Click Defense from AI Attackers
Miggo Shield generates vulnerability-specific WAF rules tailored to your applications, providing you defense against AI-powered attackers in minutes from the discovery of a new vulnerability. Powered by our runtime knowledge, WAF Copilot generates precise shields you can trust — virtually patching what’s exploitable without breaking your app.


.png)
.png)